On this day in 2026, we must acknowledge a harsh reality: "backups" are no longer a safe haven for cybersecurity, but have become the primary target for hacker attacks.
With the weaponization of generative AI (GenAI), modern ransomware (Ransomware 3.0) is demonstrating unprecedented tactical intelligence. Although the dwell time in Networking is shorter, its destructive power has multiplied. Hackers no longer just encrypt your production environment; they now prioritize seeking out and deleting backup systems, wiping out snapshots, and even poisoning backup data, leaving enterprises in a desperate situation with no way out.
In the face of such threats, traditional backup strategies have become outdated. This article will delve into the two main pillars of building modern cyber resilience: Immutable Snapshots and Physical/Logical Air-Gapped Backups.
When backup software becomes an attack surface
According to the latest market threat report, over 90% of ransomware attacks attempt to destroy backup repositories. This has driven the storage and cybersecurity market to shift their technical paradigms, moving from the traditional RTO question of “How long will it take us to recover?” to “Are we sure our data still exists?” This is because storage systems are becoming more security-focused—they are no longer just simple data repositories, but have become critical defense points with built-in ransomware detection and prevention mechanisms. On the other hand, requirements related to Networking insurance (Cyber Insurance) have already started to list “immutable backups” as a prerequisite for underwriting or claims settlement.
In the era of AI vs. AI, even if traditional perimeter defenses (Firewall/EDR) block 99% of attacks, the remaining 1% can still be fatal. Therefore, "immutable" backups data are the key advantage for enterprises to refuse to pay ransoms at the negotiation table.
Core Technology One: Immutable Snapshots
What is "immutability"?
Simply put, it means "write once, read many" (WORM - Write Once, Read Many). Once data is written and locked, within the set retention period, no one—including System Management members, Root Permission owners, or even the QES software itself—can modify or delete these data.
In recent years, due to the widespread adoption of Object Lock, Object Lock based on the S3 API has become the standard for cloud and on-premises storage objects. Many modern high-speed storage arrays (All-Flash Arrays) model now integrate this feature directly at the underlying layer, eliminating the need for additional software layers. Furthermore, the information environment has introduced multi-factor authentication (MFA) enforced deletion. Even if a hacker obtains administrator credentials and wants to modify the immutability policy or forcibly delete snapshots, the system will trigger the "Four-eyes principle," requiring multiple people and multiple factors License before approval is granted. This ensures the undeletable characteristic of data.
Technical Core II: Physical and Logical Isolation (Air-Gapped Backups, Airgap Isolation Backup)
Traditional vs. modern Air-Gap are already very different. In the past, we thought of Air-Gap as removing the tape and locking it in a safe deposit box. Although this is effective, the recovery speed (RTO) is too slow and cannot meet modern business requirements. However, it can still serve as an offsite backup node and, in the event of Networking interruption and inability to recover, act as the last line of defense.
Modern "virtual air-gap" refers more to logical isolation and Networking layer blocking, including non-routable Networking (Non-routable Networks). We can store backups in a network segment completely isolated from the production environment, and only during the scheduled backup time will a specific secure channel be opened to transfer data for backup. Once the backup is complete, this specific secure channel is immediately closed, so hackers cannot access this isolated, unreachable golden backup area.
In addition, enterprises will also implement an isolated recovery environment (Cleanroom Recovery), using cloud resources to establish a separate secure clean area. Before restoring the backup data to the production environment, AI scanning and identification are first performed in the secure area to ensure there is no hidden malicious software.
From “Manual Disconnection” to “Intelligent Isolation”: The Evolution of Airgap+ Technology in Practice
After understanding the theory behind air-gapping, the most common practical challenge enterprises face is: “Do IT staff really have to go to the server room every day to plug and unplug Networking cables?” In an era of tight manpower, this is clearly unrealistic. Therefore, a new generation of backup protection technology has introduced the concept of “Active Air-Gap,” such as QNAP’s Airgap+ technology, which automates and smartens this concept.
The core logic of this technology lies in the concept of “Disconnected by default.” Unlike traditional firewalls that rely solely on rule-based software to block traffic, the modern Airgap+ integrates backup software (such as HBS 3) with the control layer of Networkingunit (Router or Switch). Only at the moment when a backup task is initiated will the system send a command to “wake up” the specific Networking interface (Link Up); once data transmission is complete, the Networking interface will be immediately shut down at the physical or logical layer (Link Down).
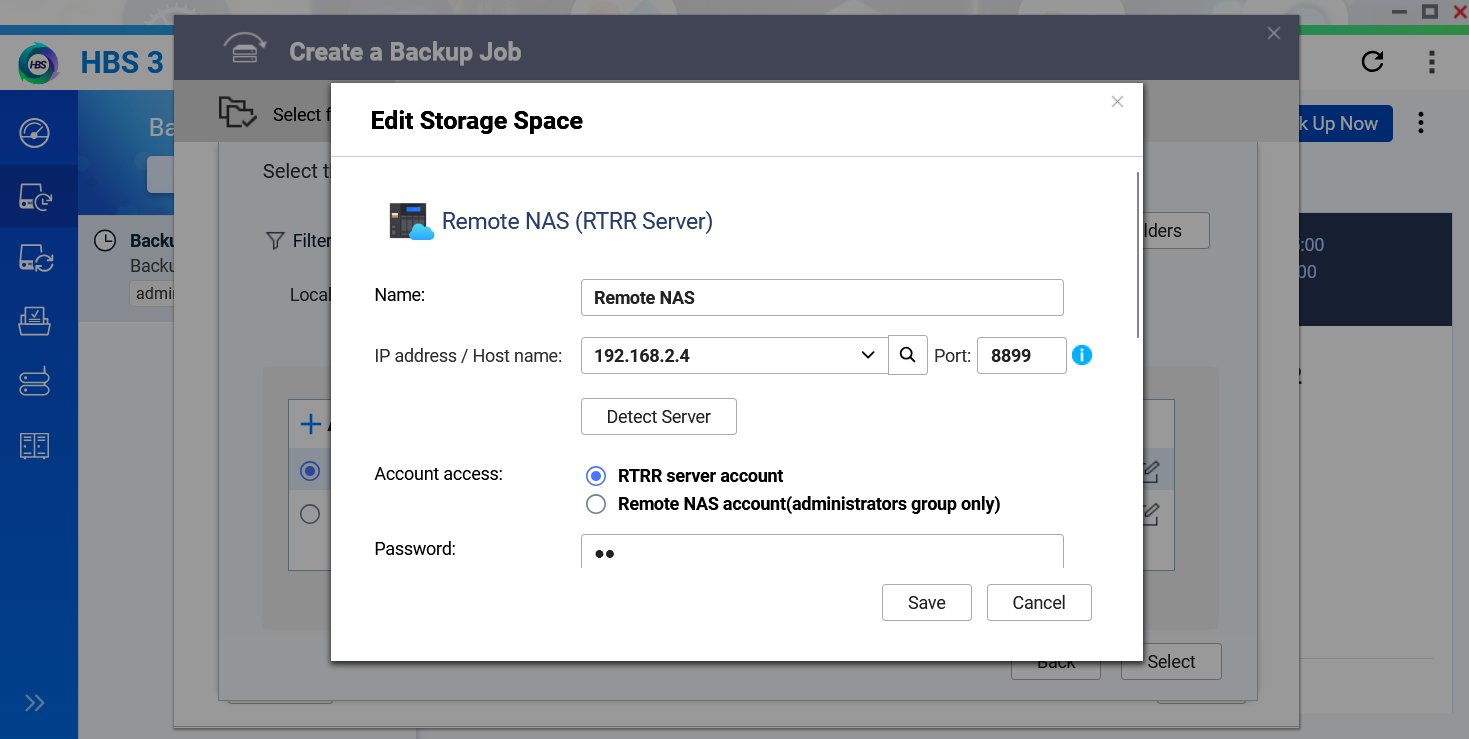
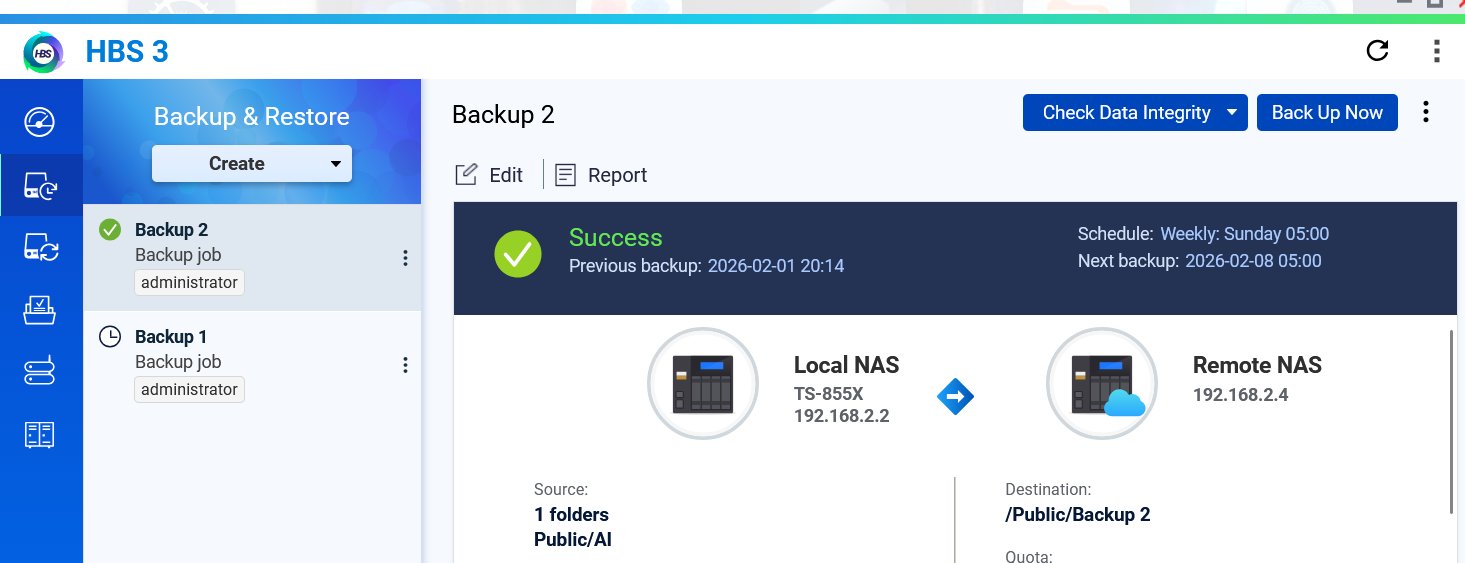
When setting up HBS backup and selecting remote NAS unit, you can conveniently enable the RTRR server. Scroll down on this page to find the Airgap+ option.
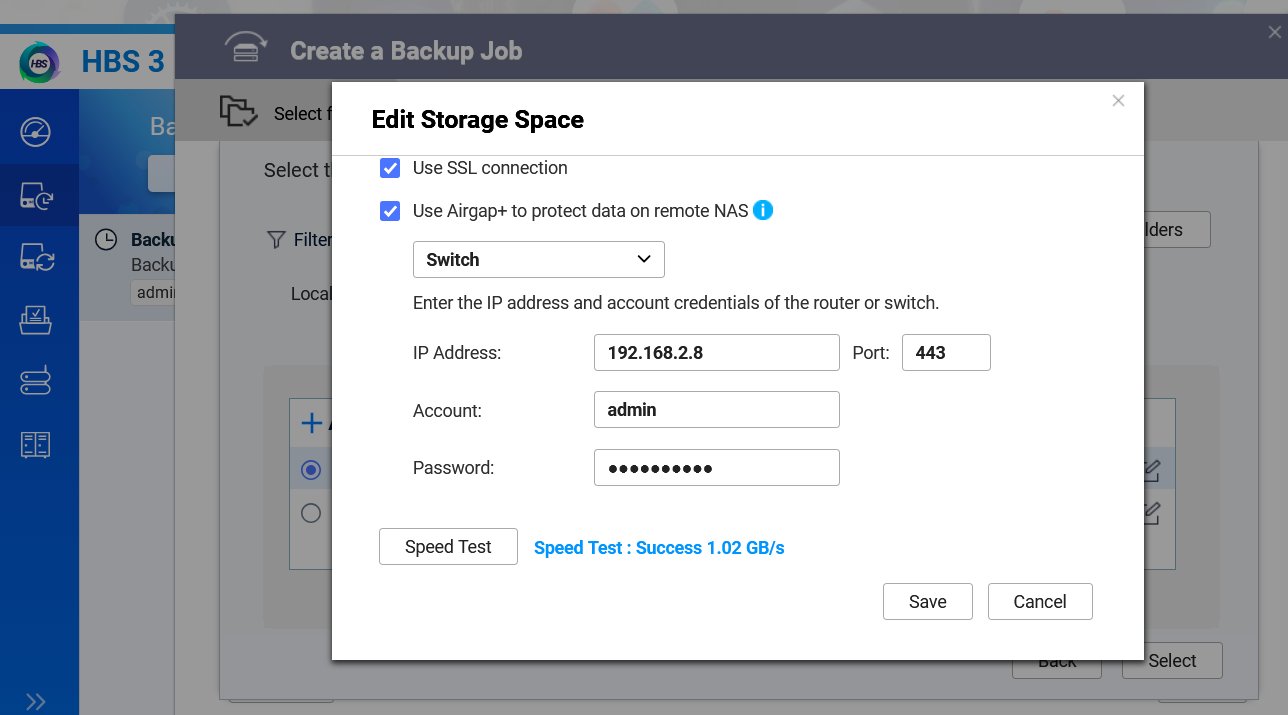
In the image, you can see that we selected a QNAP Switch supporting Airgap+. In this case, we chose the QSW-M3224-24T. You can see that the actual test speed in this case reached 1.02GB per second. The environment between the two devices is connected via 10GbE Networking, which makes the backup synchronization much more efficient.
This design creates a “time window” that is difficult for hackers to cross, because for 99% of the time, the backup server is completely invisible on Networking (Invisible), making it undetectable by scanning tools and unreachable by ransomware software. By using QNAP Router or a supported QNAP switch, you can deploy this upgraded version of Airgap+ with even higher Security isolation.
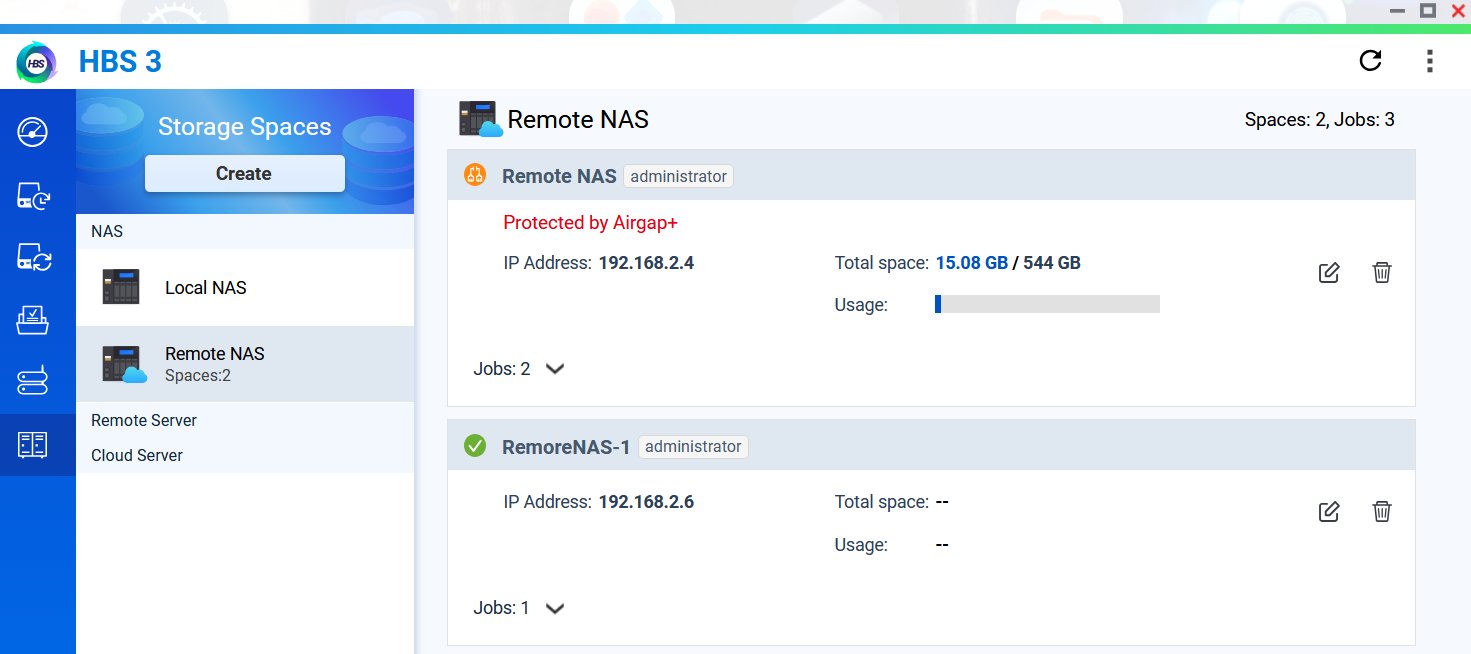
The protected NAS unit will be marked as protected in HBS 3. Even if you try to connect to this IP address, the system will not succeed, because it is hidden or blocked by Switch or Router.
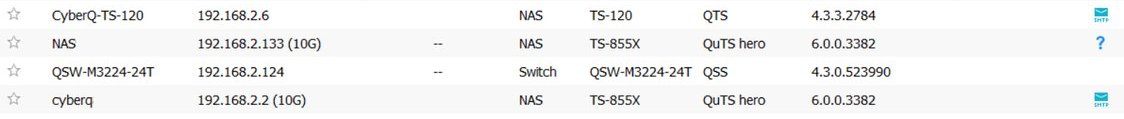
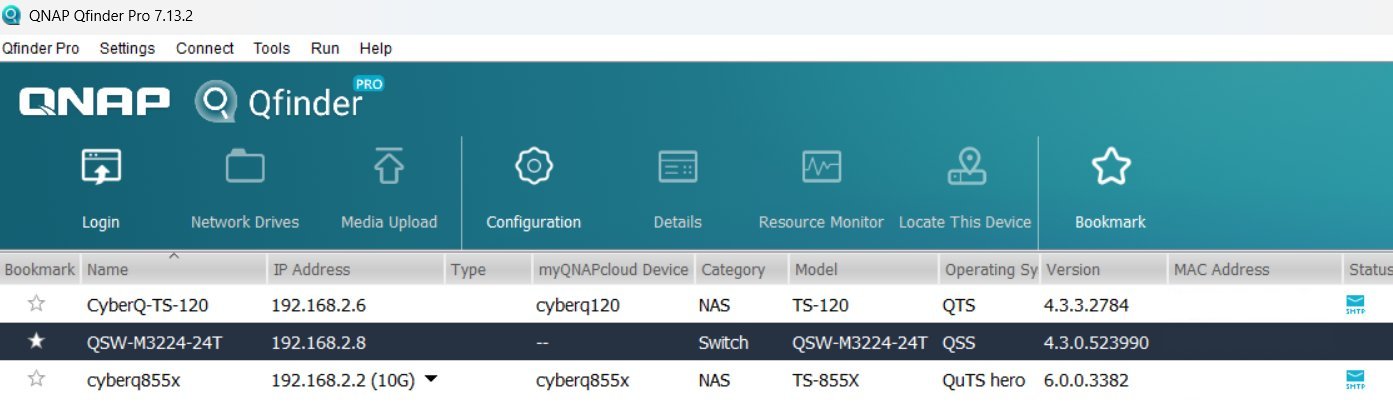
QNAP NAS unit protected by Airgap+ will not be visible on the internal network. As shown in the two images below, even QNAP's Qfinder Pro cannot find this NAS after the system backup has established the Airgap+ mechanism.
In addition, for environments with high Security requirements, an advanced architecture can even adopt the "Bridge Mode," which means we can add an intermediary bridge unit (Bridge NAS) that is not storagedata between the production environment and the backup vault. The production server can only access the intermediary unit, while the actual backup vault is hidden behind the intermediary unit, forming a "deep defense" that isolates the core backup area. Even if the production environment is completely compromised, attackers still cannot find a digital path to the core of the backup, which significantly enhances the ultimate data Security of the backup domain.
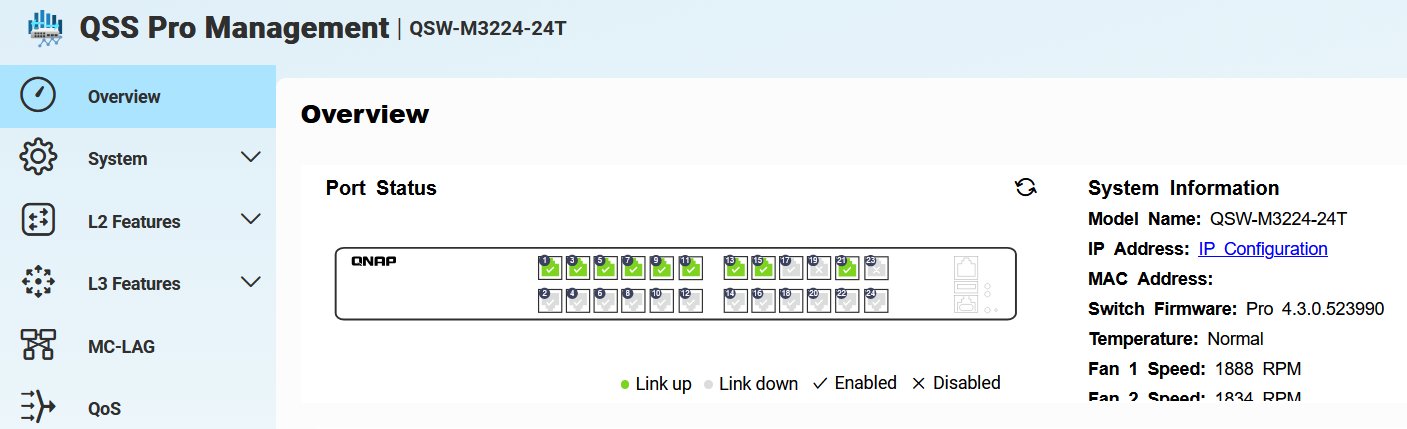
In this environment, the interface of the QNAP switch QSW-M3224-24T immediately displays that the NAS unit TS-855X is connected to ports 17, 19, and 23, all of which are shown as disconnected.
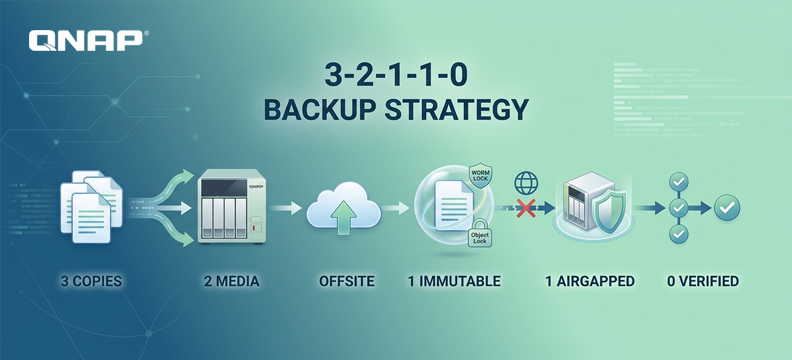
Practical strategy: Upgrade the 3-2-1 backup rule to the 3-2-1-1-0 rule
The previous “3-2-1 rule” (3 copies, 2 types of media, 1 offsite) has proven insufficient in the face of targeted attacks. Many enterprises, when implementing business information and Networking environments, have already begun to promote organizational upgrades to the “3-2-1-1-0 rule.” What is this?
That is, in an information environment, you should have at least:
3 copies of data.
2 different storage media.
1 copy to be stored off-site (Offsite).
1 offline or immutable (Offline / Immutable) copy, which is currently a key focus in the market.
0 errors (automated verification ensures backup is readable and restorable).
Trust is good, but verification and locking are more important
As the global cybersecurity landscape becomes increasingly blurred, identity verification may be stolen and vulnerabilities may be exploited by zero-day attacks (Zero-day). Only Immutable Snapshots and Air-Gap Backups provide the new generation of digital gold vaults, ensuring that in an era of rampant ransomware, enterprise core data remains intact and unharmed.