Unstoppable mutated viruses: When cloud giants also start relying on AI
A common backup method for small and medium-sized companies is to directly synchronize a large number of project files to the cloud hard disk drives. However, if one day an employee accidentally clicks on a malicious phishing email, ransomware quietly runs in the background, encrypting all files on the computer into meaningless gibberish. Without any blocking mechanism, the synchronization software will faithfully upload these “already encrypted files,” even instantly overwriting the original good backups on the cloud, causing the company’s project core assets to be wiped out in an instant.
To address this dire situation, recently Google Drive Desktop for paid Workspace users introduced a major update: AI anomaly detection and a 25-day rollback mechanism. By monitoring file change patterns on the local device with AI models, if a sudden surge of encrypted characteristics is detected, the system will immediately “hit the brakes” and temporarily pause synchronization, notifying administrators. Combined with the 25-day rollback mechanism, users can restore files. This update reveals an important trend in modern cybersecurity: backup mechanisms are evolving, moving from simple “scheduled backups” to a multi-layered defense structure that integrates real-time detection, offline isolation, and immutable protection.
Root Cause Analysis: Why is backup not equal to being securerestore?
Many IT administrators have a misconception: "I perform regular backups, so I'm not afraid of ransomware."
However, modern ransomware attack methods have evolved into highly targeted Advanced Persistent Threats (APT). They often lurk in the system for weeks or even months before launching an attack, searching everywhere for backup servers to steal Permission. The real root of the problem lies in the "propagation of contamination" and the "passivity of defense." If there is no anomaly detection, malware will infiltrate all backup pools simultaneously. This is like a car without an active collision avoidance system, where you can only rely on airbags to reduce damage after the fact.
Solution Concept: Collaboration between proactive vehicle braking and airbags
A complete modern data protection framework must be built on the collaborative relationship between “AI anomaly detection” and “data backup and recovery”:
| Defense Layer | Role Positioning | Key Indicators | Limitations |
|---|---|---|---|
| AI anomaly detection (NDR/EDR) | Active braking — cut off transmission chain | MTTD (Mean Time to Detect) | False Negative, zero-day attack |
| Backup and snapshot restore | Safety airbag — return to healthy state | RTO / RPO | If backup is contaminated, it becomes invalid |
-
AI anomaly detection (determining stop loss point): Through Networking packet analysis (NDR, Network Detection and Response) or storage I/O behavior analysis, AI instantly detects abnormal encryption and massive read/write behaviors, cutting off the transmission chain.
-
Backup and Recovery (Determines whether recovery is possible): No matter how powerful AI becomes, there will always be gaps or zero-day vulnerabilities. Having an independent Permission and a history version that cannot be tampered with is the ultimate guarantee for restoring operations.
How QNAP products solve the issue: From file monitoring to triple-layer vertical deep protection with immutable snapshots
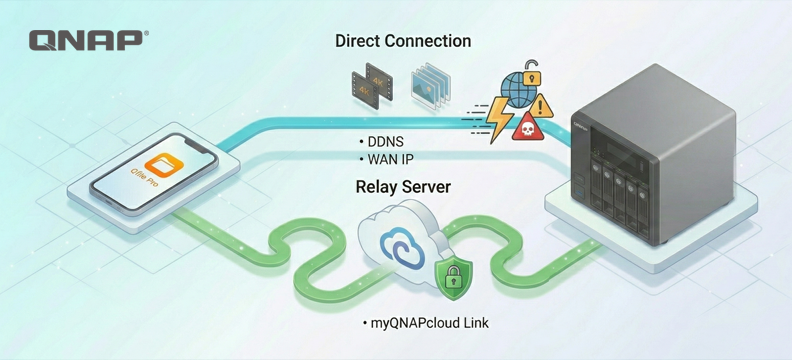
Although large-scale cloud services like Google have begun to introduce AI protection, when facing the complex internal data of large enterprises, relying solely on cloud-based paid backup solutions is not a long-term plan. QNAP directly integrates a similar "proactive detection" concept into the NAS operating system, and combines protection at the Networking layer and storage layer, forming a three-layer in-depth structure that allows enterprises' local data to also receive comprehensive protection.
First layer: storage layer real-time detection — Security Center Anomaly File Activity Monitoring. QNAP NAS is already equipped with functionality similar to Google Drive AI detection. Security Center proactively monitors file activities on NAS, and when it detects abnormal mass file modifications or encryption behaviors, administrators can instantly track the number of abnormal files within a specific time period via the dashboard, and customize security measures (protection / backup / interruption) to respond to ransomware, malicious software, or human error, minimizing data loss risk.
Second layer: Networking layer proactive blocking — QNAP ADRA NDR. In addition to file layer detection, ADRA NDR instantly monitors malicious traffic and lateral movement entering the internal network from the Networking encapsulation layer, providing alerts and blocking connections before ransomware attempts to spread to other unit, cutting off the transmission chain at the source.
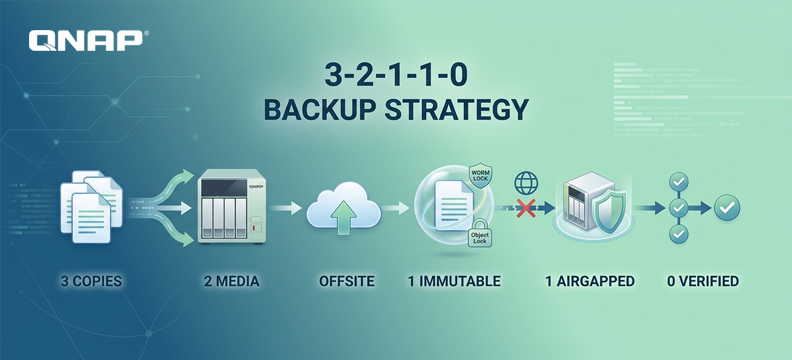
Third Layer: Immutable Backup at the Base Layer — ZFS Snapshots and WORM. Compared to cloud hard disk drives, which only provides 25 days of file version rollback, the QNAP QuTS hero operating system based on the ZFS file system offers lightweight block-level snapshots, supports immutable snapshots and WORM (Write Once Read Many) technology. Even if a hacker obtains administrator Permission, they cannot delete or tamper with historical snapshots within the locked period, ensuring that even if the first two layers of defense are breached, the enterprise still retains a clean restore point.
Quantifying benefits and environmental considerations
According to statistics from multiple cybersecurity industry reports in 2025, the average downtime for enterprises after a ransomware attack is about 24 days, while the average recovery cost excluding ransom payments is approximately $1.53 million. The total global losses caused by ransomware are projected to rise to $74 billion by 2026. Notably, organizations with immutable backup strategies can reduce their recovery time by more than 50% compared to traditional methods.
Imagine a medium-sized manufacturing or service enterprise storing its operations data on a ZFS snapshot-supported NAS unit. One day, the company is unfortunately hit by a ransomware attack. After Security Center detects the anomaly, it automatically triggers protection measures. The IT administrator immediately logs into the system and initiates a snapshot restore. Essentially, a ZFS snapshot restore is a “block pointer redirection” operation—the system only needs to redirect the block pointers of the data set to the state at the time the snapshot was taken, rather than copying or re-downloading files one by one. Therefore, regardless of whether the data size is hundreds of gigabyte or dozens of terabyte, the restore operation itself can be completed in a very short time. In contrast, re-downloading terabyte-level data from the cloud could take days. This architectural difference is expected to significantly shorten the enterprise’s RTO (Recovery Time Objective) and greatly reduce operational losses caused by downtime.
Puts security control firmly in your hands
Google Drive's introduction of AI protection is a blessing for individual users, but it also highlights the inseparable link between “detection + restoration.” For enterprises, aside from entrusting enterprise data to a cloud space that is billed per user and limited in capacity, it is even more important to choose an enterprise-grade storage protection solution with autonomous control and deeper architecture, truly building an impregnable digital data fortress.